The insidious menaces that are data breaches require a response. Do you have one prepared?
In this blog post:
- Learn why businesses need a data breach response plan (DBRP).
- Get the essential six components of a DBRP.
- Begin building your incident response framework.
Understanding the threat landscape

In the past year, the volume of interactive intrusion activity against the financial services industry increased by over 80%.
This statistic illuminates the need for accounting firms—and any other type of business that handles financial information—to be prepared for the very real probability of a cyberattack.
Data breaches are on the rise, affecting businesses across various industries. Hackers and malicious actors continually evolve their tactics, exploiting vulnerabilities in cybersecurity defenses. Understanding the threat landscape is the first step toward acknowledging the pressing need for a robust DBRP.
Data breach consequences

The fallout from a data breach is multifaceted and can have severe consequences for businesses. Financial losses, reputational damage and legal repercussions are just the tip of the iceberg.
Without a comprehensive DBRP in place, organizations risk exacerbating these consequences and jeopardizing their long-term success.
The role of a data breach response plan
The proactive versus reactive debate in cybersecurity is settled with the resounding importance of a DBRP.
A well-crafted plan not only mitigates potential damages, but also fosters resilience, ensuring that the business can swiftly recover and minimize downtime in the aftermath of a breach.
Key components of a data breach response plan

No. 1: Establish an Incident Response Team (IRT)
Identify key team members and their roles, ensuring regular training and drills to maintain preparedness.
Best practices for establishing your IRT
- Your team should be knowledgeable about cybersecurity best practices. Ensure they’re not only up to date on their security awareness training, but that they truly care about and are interested in keeping the rest of the business secure.
- The team should be ready to jump on threats and act immediately—no matter the time of day.
- Depending on the size of your organization, the IRT can be an internal task force or an outside service.
There are many reasons why businesses of all sizes should invest in an outside agency for their incident response team. (And it’s probably more affordable than you think.)
No. 2: Incident detection and reporting
Knowing about the threat? That’s pretty important. And the quicker you discover the incident, the easier the clean-up will be.
Real-time monitoring systems and protocols for reporting suspicious activities should be at the very top of your plan. Make sure everyone at your business knows where to go to report incidents promptly.
No. 3: Communication plan
No one likes to say, “Hey, we messed up,” but unfortunately, communicating that there’s been a breach is part of the job. (A very mandatory part.)
For this reason, develop an internal and external communication strategy. How will you communicate that there’s been a breach? Maintain transparency with employees, clients, partners and, of course, regulatory bodies.
Use this draft of a notice to get started. Save it somewhere secure (and impenetrable) on the off chance you need it.
No. 4: Legal and compliance considerations
Compliance with data protection regulations depends on your business type, the state of operation and the nature of the information you manage.
To navigate these intricacies, it’s crucial to understand the specific legal requirements applicable to your circumstances.
To ensure adherence to data protection regulations, get yourself some legal counsel. They can provide valuable insights into the legal landscape and guide your business in taking appropriate actions, should the need arise.
Did an incident occur? Notify the Cybersecurity and Infrastructure Security Agency (CISA) promptly by sending details to report@cisa.gov or calling 888.282.0870 within 72 hours of the occurrence. For additional information and reporting guidelines, go to cisa.gov/report.
No. 5: Data recovery and system restoration
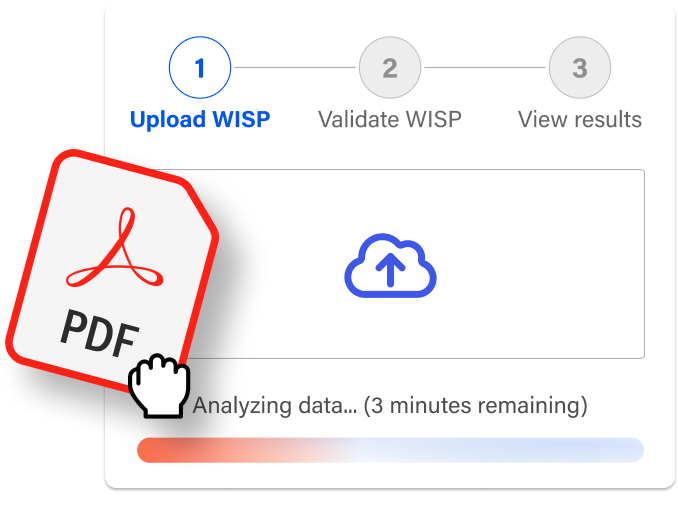
The importance of a backup and recovery plan cannot be understated.
Should you experience data loss, backups ensure that there is an uncorrupted copy of your data ready to use right away.
We have so much more on this topic—and even a few solutions to get your data backed up. Read more on the subject here.
No. 6: Regular updates and reviews
The last part of your plan? Plan to make changes to the plan.
A DBRP is not a one-time endeavor. Regular updates and reviews, aligned with industry standards and best practices, ensure that the plan remains current and effective against evolving cyberthreats.

Prioritize cybersecurity with your own DBRP
Preparedness is the key to mitigating the impact of potential breaches. And running through these “what if” scenarios regularly is essential.
You’ve worked hard to create a financially stable business and earn the trust of your clients. A DBRP—imbued with solutions that bolster your organization—will preserve the reputation you’ve helped build.
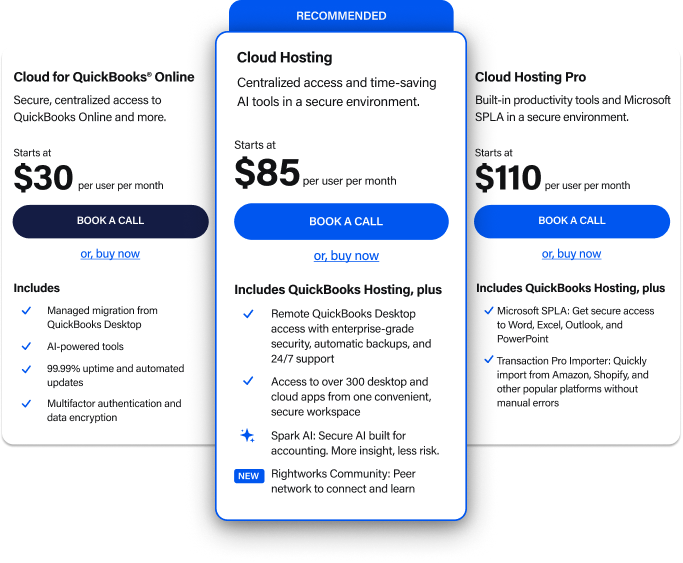
Get help supplementing your own DBRP to keep your business backed up, secure and safer from threats with Rightworks today.