Cybersecurity remains one of the most critical challenges for businesses today, especially for those handling sensitive financial information. Understanding and implementing proper security measures is no longer optional—it’s essential for protecting your firm, your clients, and your reputation.
Effective security begins with understanding the terminology and concepts that form the foundation of cybersecurity practices. Before diving into practical scenarios, let’s test your knowledge of essential cybersecurity terms that every professional should recognize.
Now that we’ve explored your familiarity with cybersecurity terminology, let’s apply that knowledge to real-world scenarios. The following assessment will test your understanding of key security best practices that can help safeguard your organization against common threats.
- Question 1: Password Security Best Practices
- Question 2: Authentication Security
- Question 3: Email Security
- Question 4: Social Media Best Practices
- Question 5: Transferring Personal Information
- Security Awareness: A Critical Defense Layer
- Building a Stronger Security Posture
Free Download → The Ultimate Cybersecurity Guide for Accountants
Question 1: Password Security Best Practices
Which of the following is a security best practice?
- Using a password manager.
- Storing passwords in your web browser.
- Using the same password for multiple accounts.
- Writing down passwords and keeping them in your desk.
Important considerations for password security:
- Popular web browsers often have security vulnerabilities that put stored passwords at risk.
- Hackers specifically target browser password stores because they contain credentials for multiple sites.
- With the numerous applications requiring authentication today, a dedicated password manager offers significantly better security than browser storage.
Answer: 1. Using a password manager.
Question 2: Authentication Security
Which of the following is a security best practice?
- Sharing login credentials with trusted colleagues.
- Protecting data with a username, password, and multifactor authentication.
- Using the same email for personal and work accounts.
- Changing passwords only when required.
Sharing passwords creates unnecessary security risks, regardless of how trusted colleagues may be. Personnel changes happen regularly, and proper authentication should include:
- A username: Typically, an email address specific to the context (work email for work applications)
- A strong password: Using a combination of characters, numbers, uppercase, lowercase, and symbols
- Multifactor authentication (MFA): Adding an additional layer of security beyond the password, such as a verification code or biometric confirmation
Answer: 2. Protecting data with a username, password, and multifactor authentication.
Free Download → The Ultimate Cybersecurity Guide for Accountants
Question 3: Email Security
Your colleague sends you an email with an attachment you weren’t expecting. What’s the security best practice?
- Open it since you know the sender.
- Reply to the email to confirm they sent it.
- Call the sender to verify they sent you the attachment.
- Delete the email immediately.
Business email compromise (BEC) is a sophisticated threat where attackers gain access to legitimate email accounts and use them to request file opens or transfers. According to the FBI, BEC is one of the most financially damaging online crimes.
When receiving unexpected attachments, verifying through a different communication channel is the only secure approach. Email responses can still be intercepted if the account is compromised.
Answer: 3. Call the sender to verify they sent you the attachment.
Question 4: Social Media Best Practices
Which of the following social media captions is the most secure?
- “My cat Sirius turned 5 today!”
- “Woman’s best friend.”
- “Celebrating at my alma mater today!”
- “Birthday time with Mama Jane!”
The FBI advises against sharing personal information that could be used to answer security questions or build a profile for social engineering attacks. Information to protect includes:
- Pet names
- Educational institutions attended
- Employment history
- Birth dates
- Family members’ names
- Personal preferences (favorite movies, books, etc.)
Answer: 2. “Woman’s best friend.”
Free Download → The Ultimate Cybersecurity Guide for Accountants
Question 5: Transferring Personal Information
A client needs to share personal information with you for tax preparation. What’s the most secure way to receive this information?
- Have them come to your office in person.
- Ask them to email it to you.
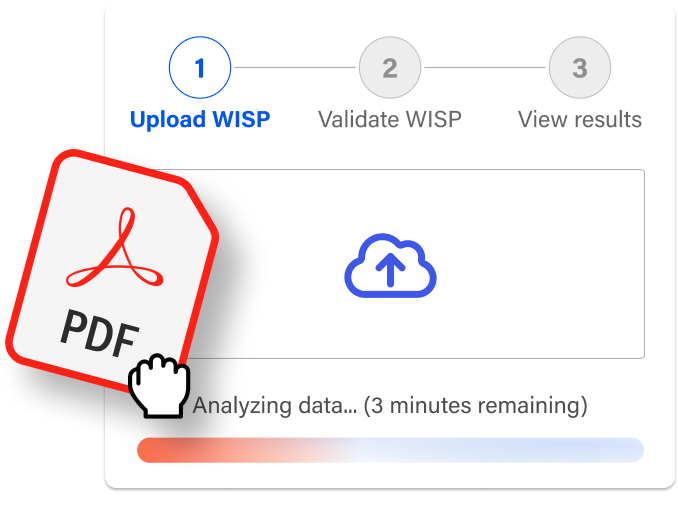
- Give them their own unique username and password to your cloud portal—insist they enable MFA—then have them fill out the information themselves.
- Have them read the information to you over the phone.
While in-person meetings provide security, they’re often impractical and limit your service area. Secure client portals offer the optimal balance of security and efficiency by:
- Providing encrypted communication channels.
- Enabling direct client input, reducing transcription errors.
- Implementing proper authentication protocols.
- Creating audit trails of information submission.
Answer: 3. Give them their own unique username and password to your cloud portal—insist they enable MFA—then have them fill out the information themselves.
Security Awareness: A Critical Defense Layer
According to Verizon’s latest Data Breach Investigations Report, 74% of breaches involve the human element. This statistic highlights that three-quarters of security incidents stem from:
- User errors
- Privilege misuse
- Credential theft
- Social engineering attacks
Comprehensive security awareness training significantly reduces these risks by preparing staff to recognize and respond appropriately to potential threats.
Free Download → The Ultimate Cybersecurity Guide for Accountants
Building a Stronger Security Posture
No organization is immune to security threats, but these measures significantly improve your security posture:
- Implement structured security awareness training: Provide regular, comprehensive training for all staff members regardless of position or technical expertise.
- Partner with specialized technology providers: Work with IT security partners who understand your industry’s specific requirements and compliance needs.
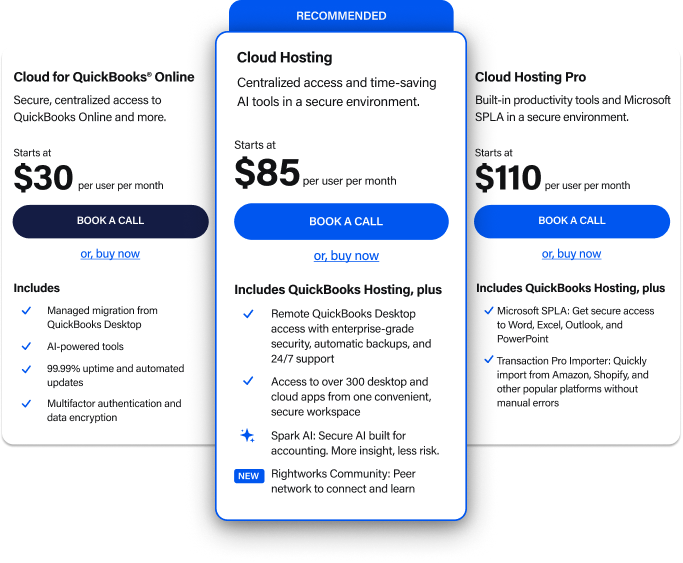
- Leverage secure cloud solutions: Managed cloud environments often provide superior security to on-premises systems while offering flexibility, disaster recovery, and collaboration benefits.
- Develop and test response plans: Create documented procedures for security incidents that clearly outline responsibilities and recovery steps.
Security isn’t about perfection—it’s about establishing reasonable protections, maintaining vigilance, and being prepared to respond effectively when incidents occur. By improving your cybersecurity knowledge and implementing appropriate measures, you significantly reduce your organization’s risk exposure.
Take the next step toward strengthening your security posture by scheduling a consultation with our security experts. Our team can help assess your current security measures and identify practical improvements that align with your business needs.
For more information about securing your accounting firm or small business, subscribe to our blog today.