Accounting firms are prime targets for cybercriminals for obvious reasons: you maintain a treasure trove of sensitive financial information, personal data, and valuable client records. As guardians of sensitive information, it’s on you and your team to create a culture of security awareness and implement robust protection measures.
In this post, discover the most pressing security threats facing accounting firms today, what experts are predicting is on the horizon, and how to stay safe from them all.
Table of Contents
Future Cybersecurity Predictions for Accounting Firms
-
- 1. Deepfakes Will Become the Primary Phishing Threat
- 2. Ransomware Will Evolve from Data Encryption to System Destruction
- 3. Remote Work Security Will Become a Top Compliance Priority
- 4. Government Regulations Will Intensify for Financial Data Protection
- 5. Security Vendor Consolidation Will Accelerate
- 6. Third-Party Risk Assessment Will Become Standard Practice
- 7. Security Culture Will Become a Competitive Differentiator
Current Top Security Threats Facing Accountants
1. Sophisticated Phishing Attacks
Phishing remains one of the biggest cyberthreats facing accounting firms today. These attacks have evolved far beyond obvious spam emails with poor grammar. Modern phishing attempts use spoofed email addresses that appear legitimate, creating urgent scenarios that play on emotions and prompt hasty actions.
Hackers are becoming increasingly sophisticated, employing tactics like:
- SMS phishing (smishing) to trick recipients into clicking on malicious links.
- Voice phishing (vishing) using fake calls from “financial institutions”.
- AI-generated communications that mimic trusted contacts.
- Targeted spear-phishing campaigns customized to accounting professionals.
These attacks often lead to ransomware infections, which prevent firms from accessing data until a ransom is paid—with no guarantee that data will be returned intact.
What You Can Do →
- Implement email authentication protocols like DMARC, SPF, and DKIM to filter out spoofed emails.
- Train employees to verify sender details by checking the actual email address, not just the display name.
- Establish verification procedures for any requests involving financial transactions or sensitive information.
- Install advanced email security tools that use AI to detect sophisticated phishing attempts.
- Create a culture where employees feel comfortable reporting suspicious communications without fear of reprimand.
2. DIY Remote Workspaces
Many accounting firms have transitioned to remote or hybrid work models without implementing adequate security measures. Home networks, personal devices, and public Wi-Fi connections create multiple attack vectors that cybercriminals can exploit.
Remote work security challenges include:
- Unprotected home networks with default router passwords.
- Personal devices without proper security controls.
- Insecure file-sharing practices.
- Physical security risks in public spaces.
- Inconsistent security policy enforcement.
What You Can Do →
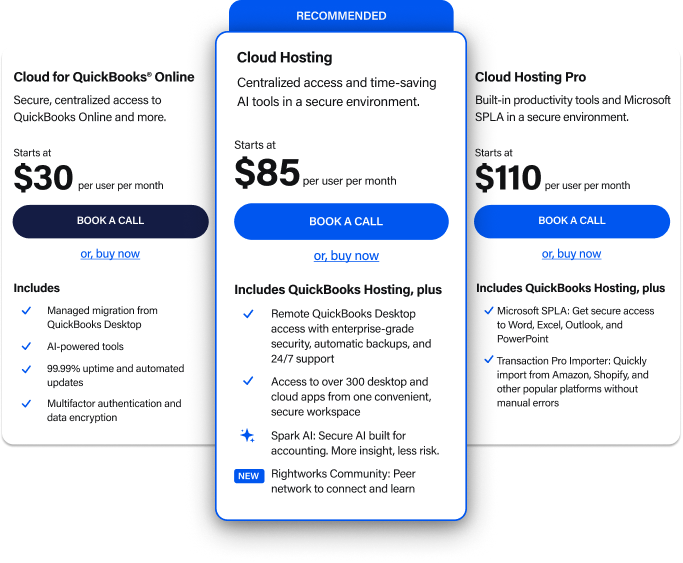
- Transition to secure cloud solutions that provide 24/7/365 protection for your sensitive data.
- Implement multifactor authentication (MFA) for all applications containing personal data.
- Ensure all devices have current antivirus software and automatic security updates.
- Develop and enforce a comprehensive remote work security policy that includes:
- VPN requirements for accessing company resources.
- Prohibition on using public Wi-Fi without proper protection.
- Guidelines for secure home office setup.
- Device encryption requirements.
- Regular security compliance checks.
3. Insufficient Encryption Practices
Many accounting firms fail to implement comprehensive encryption across all communication channels and devices. Without proper encryption, sensitive financial data becomes vulnerable to interception and theft during transmission or when stored on devices.
Common encryption oversights include:
- Unencrypted email communications containing sensitive data.
- Failure to use secure client portals for document exchange.
- Unencrypted mobile devices with client information.
- Lack of encryption for external storage devices.
- Unsecured connections for remote access.
What You Can Do →
- Ensure end-to-end encryption for all client communications and data transfers.
- Verify website security by confirming HTTPS connections and valid security certificates.
- Encrypt all devices, including computers, tablets, and smartphones that access client data.
- Disable Bluetooth and other wireless protocols when not in use, especially in public settings.
- Implement a secure file-sharing solution like SmartVault Accounting Pro or a dedicated firm portal instead of email attachments.
- Use encrypted backup solutions to protect archived data.
4. Inconsistent Security Training
Without regular, updated security training, employees become the weakest link in your security infrastructure. A single uninformed action, like clicking a malicious link or downloading a compromised attachment, can compromise your entire firm’s security.
Training deficiencies often include:
- One-and-done security training instead of ongoing education.
- Failure to address emerging threats.
- Lack of practical application scenarios.
- Absence of testing to verify knowledge retention.
- No feedback mechanisms for security concerns.
What You Can Do →
- Invest in ongoing security awareness training that evolves as threats change.
- Implement simulated phishing programs to test employee awareness and provide teachable moments.
- Conduct regular security refreshers rather than annual training sessions.
- Develop role-specific security training that addresses the unique risks different team members face.
- Create clear security incident reporting procedures and encourage their use.
Free Download → The Ultimate Cybersecurity Guide for Accountants
5. Third-party Vulnerabilities
Your security is only as strong as your weakest vendor. Many accounting firms focus on internal security measures while overlooking the significant risks posed by third-party providers with access to their systems or data.
Third-party security risks include:
- Software vendors with inadequate security practices.
- Cloud providers without proper compliance certifications.
- Delayed security updates for on-premises software.
- Insufficient data handling agreements.
- Lack of vendor security assessments.
What You Can Do →
Vet third-party vendors thoroughly before engagement, reviewing their security practices and compliance certifications, and prioritize cloud-based applications that can deploy security updates in real-time.
Establish minimum security requirements for all vendors, including:
- Strong authentication practices
- Regular security audits
- Encryption standards
- Data handling procedures
- Incident response protocols
Include security requirements in contracts with specific SLAs for security updates and breach notifications. Then, regularly review vendor security practices as part of your firm’s risk assessment process.
Top 7 Cybersecurity Predictions
While addressing current threats is essential, forward-thinking accounting firms must also prepare for emerging challenges. Here are seven critical cybersecurity predictions to help you future-proof your practice:
1. The Deepfake Era
AI phishing threats will become more common—and convincing.
More and more cybercriminals are using deepfake technology to carry out phishing attacks. These aren’t your standard phishing emails (though you still need to be prepared to defend against those, too).
Deepfake phishing can convincingly mimic voices and videos, making it difficult to distinguish between real and fake communications. In fact, according to a report by Onfido, injection attacks—a common deepfake fraud method—have increased 40% year over year, making multi-layered fraud prevention more critical than ever.
What You Can Do →
- Implement robust identity verification processes. Always verify requests through live voice or video calls.
- Educate employees about the dangers of phishing attacks, deepfakes, and social engineering tactics, and reinforce the importance of verifying unusual requests.
2. The Rise of Ransomware
Sophisticated hackers will stop at nothing to extort sensitive data.
Ransomware remains a significant threat, with new variants capable of encrypting data and destroying systems and hardware. This evolution demands an enhanced response strategy.
What You Can Do →
- Conduct regular employee training to help your staff recognize phishing attempts, which often lead to ransomware attacks.
- Implement strong password policies, multifactor authentication (MFA), and biometrics to secure access to data.
- Develop a comprehensive backup and recovery strategy to ensure quick restoration of data in case of an attack.
Free Download → The Ultimate Cybersecurity Guide for Accountants
3. The Quest For Remote Security
To stay compliant, teams will need to defend client data everywhere.
The shift to more remote and hybrid work has been a double-edged sword. While it offers flexibility and operational continuity, it also exposes remote employees (and businesses) to vulnerabilities, particularly due to unsecured home networks and devices.
As businesses continue to adapt to more remote and hybrid teams, ensuring secure systems and compliance with regulations remains imperative.
What You Can Do →
- Partner with a cloud solution provider that offers 24/7 data protection, ensuring that sensitive information is continuously monitored and safeguarded against unauthorized access.
- Equip your staff’s remote devices with updated security software. Ensure all remote devices (laptops, tablets, smartphones) are updated regularly and equipped with the latest antivirus software.
- Use virtual private networks (VPNs) to encrypt data transmitted over the internet. VPNs create a secure tunnel between individual devices and a business’s resources, protecting sensitive information from being intercepted by cybercriminals.
4. Government Regulations Will Intensify
Cybersecurity regulations will keep changing…and changing…and changing…
Any business handling sensitive financial and personal client data must comply with stringent government regulations. And as technology advances, and cybercriminals advance with it, regulatory bodies will continue to update and expand their requirements, too.
What You Can Do →
- Stay informed about changes in regulations and ensure compliance with frameworks such as the IRS Security Six and the FTC Safeguards Rule, among others.
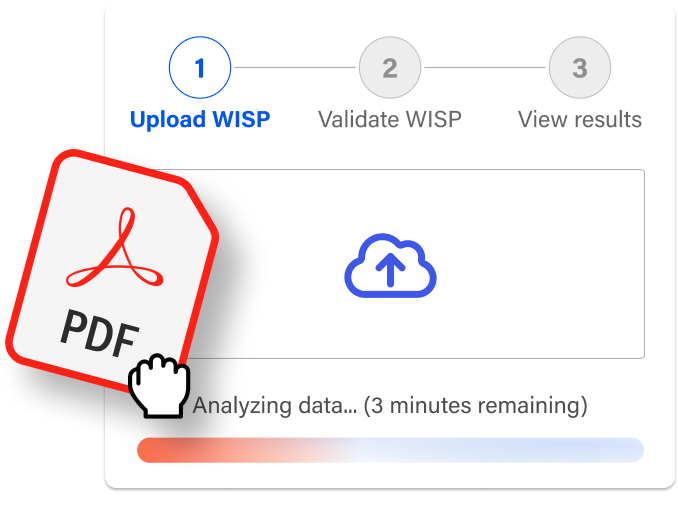
- Ensure that you have a Written Information Security Plan (WISP) that aligns with regulatory requirements. Check yours now.
- Conduct regular compliance audits of your security policies and procedures to help identify areas where compliance may be lacking.
- Partner with a security provider who can help you create a WISP, identify security gaps, adapt to regulatory changes, and streamline and manage compliance on your behalf.

5. Security Vendor Consolidation Will Accelerate
Gartner predicts that by 2025, 80% of enterprises will adopt a strategy to unify web, cloud services, and private application access from a single vendor’s SSE (security service edge) platform. This approach can enhance security efficiencies, reduce complexities, and lower costs.
What You Can Do →
- Evaluate potential security partners that offer comprehensive security services, including a managed cloud and a full slate of security offerings.
- Conduct a comprehensive audit of existing security tools and processes to identify redundancies and gaps.
- Develop a phased implementation plan that minimizes disruption.
6. Third-Party Risk Assessment Will Become Standard Practice
Third-party vendors can pose significant security risks.
Once again, Gartner predicts that, by 2025, 60% of organizations will use cybersecurity risk as a primary determinant in conducting third-party transactions and business engagements. Are you considering how secure the companies you do business with are? After all, you’re only as safe as your riskiest vendor.
What You Can Do →
- Conduct thorough due diligence and ongoing monitoring to assess the cybersecurity practices, compliance, and risk management of third-party vendors.
- Implement strong, contractual safeguards and technical controls with contracts that include data protection requirements.
- Involve third-party vendors in your incident response planning, establish protocols for identifying anomalies, and consider using managed security service providers for enhanced protection.
7. Security Culture Will Become a Competitive Differentiator
Creating a healthy security culture will become even more critical. Regular education, training, and updates on the latest cybersecurity threats will empower employees to act as your first line of defense.
A strong security culture promotes awareness and accountability, which is key to helping employees identify and mitigate risks before they escalate into major incidents.
What You Can Do →
- Invest in continuous security awareness training programs that include simulations of phishing and social engineering attacks.
- Encourage open communication about potential security threats and foster an environment where employees feel comfortable reporting suspicious activities.
Free Download → The Ultimate Cybersecurity Guide for Accountants
Next Steps: Securing Your Accounting Firm
While there’s no such thing as zero security risk, implementing a comprehensive security approach significantly reduces your vulnerability. Remember that employee awareness remains your biggest asset in protecting sensitive data.
To get started:
- Create or update your Written Information Security Plan. Use our free WISP Analyzer and get your action plan to better protection.
- Schedule a security risk assessment to identify vulnerabilities specific to your practice.
- Explore our cloud security solutions designed specifically for accounting firms.
Ready to strengthen your firm’s security posture? Schedule a consultation today to discuss your specific needs and develop a customized protection plan for your accounting practice.