For accountants and business owners, understanding the dark web is crucial. With sensitive financial data, client information, and proprietary business intelligence at stake, the dark web poses significant risks to your firm’s security and reputation.
In this post, I’ll explore all these questions, clarify what the dark web is, provide practical advice about protecting your business from having its information sold there, and more.
Table of Contents
- What Is the Dark Web?
- Why the Dark Web Matters for Businesses
- 6 Facts About the Dark Web
- Key Takeaways
What Is the Dark Web?
The dark web is a part of the internet that requires special software to access and is intentionally hidden from standard search engines. Unlike the surface web (what you access through Google or Bing) or even the deep web (password-protected sites like your bank account), the dark web is designed for anonymity.
While the dark web itself isn’t inherently illegal, it does provide a platform where illegal activities can take place with greater anonymity. This includes marketplaces selling stolen personal information, credentials, and other illicit goods or services.
Why the Dark Web Matters for Businesses
Understanding the dark web is crucial because it directly impacts your business security and financial health. When data breaches occur, your stolen information often ends up for sale on dark web marketplaces before you even realize you’ve been compromised.
For accounting firms and businesses, the stakes are particularly high. Compromised credentials could lead to:
- Unauthorized access to financial systems and client data
- Theft of sensitive financial records and tax information
- Corporate espionage and intellectual property theft
- Ransomware attacks that lock you out of critical systems
- Identity theft (affecting employees and clients)
- Significant financial losses that can reach millions of dollars
- Severe reputational damage and loss of client trust
- Legal liabilities and regulatory penalties
Research shows that a single data breach resulting from dark web activity can lead to multimillion-dollar losses, legal repercussions, and long-term reputational harm. What’s particularly concerning is that sensitive business data is often sold on the dark web before businesses even realize they’ve been compromised.
By recognizing what the dark web is and how it operates, you can take proactive steps to protect your business information and respond appropriately if your data is compromised.
6 Facts About the Dark Web
1. The Internet Has 3 “Sections”: Deep Web, Dark Web, Surface Web
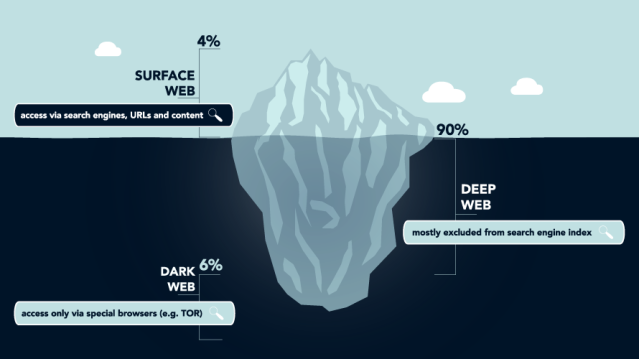
The internet is comprised of these three different “sections”:
- Surface web: What is searchable and indexed by sites like Google and Bing
- Deep web: “Refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine” (CSO Online)
- Dark web: A small portion of the deep web that requires specialized software to access
The deep web includes paywall-only content and content that requires sign-in credentials, like medical records, membership websites, and confidential corporate web pages. It comprises much of the internet.
Although people don’t use the dark web exclusively for illegal purposes, it is known as the marketplace for birth dates, social security numbers, and bank account numbers. And that brings us to fact number two.
2. The Dark Web Is Where Criminals Buy, Sell, and Trade Stolen Credentials
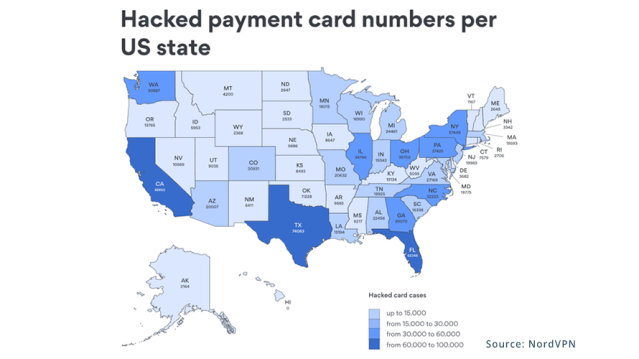
So much personal information is readily available on the internet. And the information you want to keep private—credit card numbers and social security numbers—can easily be stolen, sold, bought, and traded.
Even if your credit card never leaves your wallet, someone could have a copy of it. Credit card information can be picked up via a scanner while you’re walking through the grocery store. In the U.S. alone, there are 1.6 million card numbers for sale.
For businesses, the risks are even more alarming. Recent investigations by cybersecurity researchers have revealed that access to entire business systems is being sold on the dark web at shockingly low prices. For example, admin-level access to accounting firms has been auctioned off for as little as $600, while VPN credentials to law firms have been spotted for similar amounts.
What makes these sales particularly dangerous is that the buyers gain full control over business networks, including:
- Accounting systems with client financial data
- Tax preparation software
- QuickBooks and other financial platforms
- Employee login credentials
- Client contact information
- Banking details and routing numbers
In one documented case, a cybercriminal sold access to a U.S. accounting firm’s systems on a dark web marketplace, complete with detailed instructions on how to exploit an unpatched vulnerability that had existed for years. The buyer of such credentials would have immediate access to the entire client database and financial records.
3. The “Attack-as-a-Service” Economy Makes Cybercrime Accessible
A concerning trend on the dark web is the rise of the “attack-as-a-service” economy, where cybercriminals offer ready-to-use hacking tools and services that target businesses. This has created a marketplace where even individuals with minimal technical knowledge can launch sophisticated attacks against accounting firms and businesses.
Research has uncovered several alarming offerings:
- Ransomware-as-a-Service (RaaS): Complete ransomware packages with user-friendly interfaces that allow criminals to target businesses and demand payment to unlock encrypted files.
- Exploit kits targeting outdated software: Tools specifically designed to exploit unpatched vulnerabilities in common business software, including accounting applications and remote access tools. One recent investigation found that over 15% of dark web listings offered access to organizations through vulnerabilities that had been disclosed years ago.
- Phishing campaign services: Customizable phishing operations targeting specific industries, complete with convincing email templates designed to look like accounting software logins, tax agencies, or financial institutions.
- Remote access trading: Marketplaces selling Remote Desktop Protocol (RDP) and Virtual Private Network (VPN) credentials, giving buyers complete control over business networks. In one case, admin-level RDP credentials for an accounting firm were auctioned for $1,800.
4. How to Keep Your Information Off the Dark Web
There’s no guaranteed method for preventing your information from entering the dark web, but that doesn’t mean you can’t try.
Here are a few ways to protect your business information from being leaked:
- Never email sensitive information: If you must share financial data, tax information, or account numbers, do so through secure channels. Before sharing sensitive information, ask yourself: Do I know the individual asking? Do I trust this institution? Don’t be afraid to ask questions about the intended use. It’s YOUR business information, after all.
- Practice good password hygiene: Don’t share passwords, don’t reuse passwords, and change passwords often. Implement a company password policy that requires strong, unique passwords for all business accounts. Get more practical password hygiene tips here.
- Don’t visit or buy things from unsecured sites: Unsecured sites are sites without the “s” at the end of http. Always check to ensure the sites you visit contain that “s” (https:) or secure socket layer (SSL). The SSL certificate helps secure information such as login credentials, credit card transactions, bank account information, and much more.
- Use multifactor authentication: Multifactor authentication verifies your identity post-login and pre-access. This means that even if someone steals your credentials, the perpetrator wouldn’t be able to access the program they’re targeting. Instead, you would get a notification (usually via phone) that asks you if you are trying to log in. If you’re not, you click “deny” to block the intruder from entering.
- Implement a data classification system: Identify which business information is most sensitive and establish appropriate controls for each type of data.
- Conduct regular security training: Ensure all employees understand the risks of data theft and are trained to identify phishing attempts and other social engineering tactics.
5. You Can Monitor Whether Your Information Has Been Leaked
There are ways to determine if your business information is on the dark web. Security providers offer dark web monitoring services specifically designed for businesses. However, not all dark web monitoring services are created equally. At the very least, find a service offering 24/7/365 scanning and monitoring for illicit activity related to your domain and brand.
Here’s how it may look if your monitoring service finds something:
- You run XYZ Accounting Firm and use the domain @xyzcpas.
- One day, your email address appears on a dark web website.
- Your dark web monitoring service is alerted (then, they alert you.)
- You change your email password, enable multifactor authentication (if you haven’t already), and check your accounts for unusual activity.
Dark web monitoring is essential for early threat detection. Tools that scan forums and marketplaces can identify leaked credentials or proprietary files in real-time, enabling businesses to act quickly by changing passwords or revoking access before cybercriminals exploit vulnerabilities.
For accountants and business owners, this risk is magnified. If your practice management software credentials or client portal access is compromised, attackers could:
- Access sensitive client tax returns and financial statements
- Steal banking information and initiate fraudulent transactions
- Download your entire client database for identity theft purposes
- Plant ransomware that locks you out of your own systems
- Monitor your communications to gather intelligence for future attacks
With dark web monitoring, you can detect these threats early and take immediate action before damage occurs.
6. There Are Steps to Take After Your Data Has Been Leaked
If your information is on the dark web, you’ll want to act fast. Your exact actions will depend on the specific information found, but it’s safe to say that practicing all of these steps for your compromised accounts is smart:
- Change your passwords.
- Use multifactor authentication.
- Go through your recent debit card and credit card transactions.
- Notify your credit/debit card provider if any transaction seems suspect (then request a new card).
Beyond these steps, it is your responsibility to be proactive about your data privacy and security:
- Stay aware of the latest security threats and attack tactics.
- Getting a third party to help identify where your business may be vulnerable.
- Creating an information security plan.
Key Takeaways About the Dark Web
While you can’t completely prevent your information from being leaked, you can take proactive steps to protect your business and monitor for potential threats.
Remember these key points:
- The dark web is where stolen credentials and business data are bought and sold at alarmingly low prices.
- Intellectual property and sensitive financial information are prime targets.
- The “attack-as-a-service” economy makes sophisticated attacks accessible to non-technical criminals.
- You can’t guarantee your information will stay off the dark web.
- Dark web monitoring services provide early warning of compromised data.
- There are specific steps to take if your business information is compromised.
Stay informed, stay cautious, and start implementing the security practices mentioned above to significantly reduce your risk of becoming a victim of dark web activities. For accounting firms and businesses handling sensitive financial data, these precautions aren’t optional—they’re essential.
For more security information, visit us here, or better yet, schedule a risk assessment for your business today.
Subscribe to our blog for more cybersecurity tips and insights for accountants and business owners delivered straight to your inbox.