Anyone Can Protect Against Cyber-Threats With Cloud Hosting
Chances are, you didn’t become an accounting professional to learn everything there is to know about cybersecurity.
And, why should you have to?
Cloud hosting providers work tirelessly to ensure that your accounting and business applications stay secure and the financial information they hold remains confidential, so when you get to work, you can work. It’s that simple.
Using cloud hosting technology is the first and most effective measure for securing your sensitive, business-critical data.
Our longtime customer, Jeff Siegel (CEO of Siegel Solutions, a premier bookkeeping, consulting and accounting software firm), said it best:
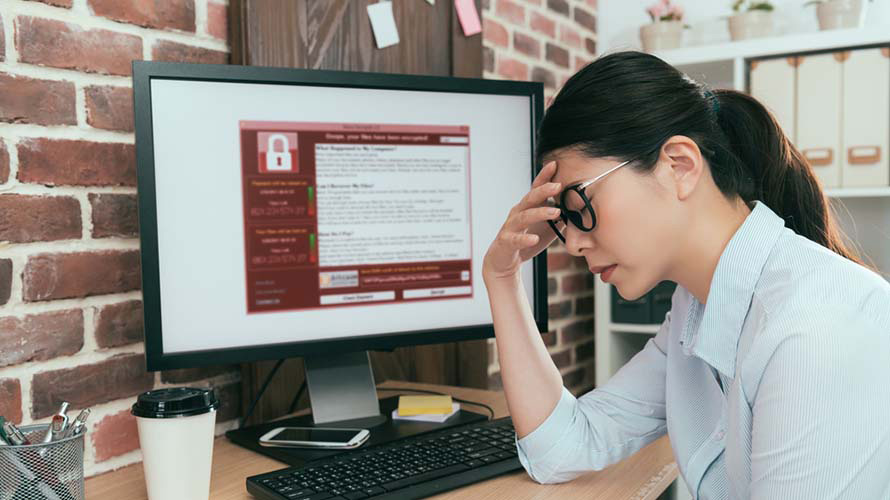
“Working in the cloud gives me peace of mind when it comes to hacks, ransomware, hardware failures, accidentally deleting a file and other issues.”
– Jeff Siegel, CEO, Siegel Solutions
Keep reading to get an overview of how our cloud technology safeguards software, apps and data using six highly-effective security protocols.
6 Ways Cloud Technology Protects Data
Below are six ways in which cloud technology keeps customer data confidential. When researching cloud providers, make sure that any company you’re vetting has all of these security protocols covered—at a minimum.
1. Cloud Providers Scan For External Threats Using Anti-Virus Software
Anti-virus software is software that automatically scans a computer for external threats.
To stop viruses from entering the Right Networks environment, our security team:
- Monitors external threats
- Scans incoming data
- Vets every hosted application for vulnerabilities (before it’s granted access into our cloud)
2. Multi-Layered Firewalls Create an Impenetrable Cloud Fortress
Firewalls serve as a protective barrier between a computer and/or network and the internet.
Right Networks (along with other reputable hosting providers) have more than a firewall. We have multi-layered firewalls. Our other robust physical and systemic fortresses include:
- Biometric scanning
- 24x7x365 onsite security guards
- Key shuffling systems
- Bastion host configurations
- …a lot more
3. Multi-Factor Authentication Confirms a User’s Identity
Two-factor authentication (or multi-factor) is a multi-step authentication system that requires users to verify their identity with a username and/or password as well as another identifying factor.
We entrust Duo, the leading multi-factor authentication program in the security industry, to verify our users’ identities.
4. Data in the Cloud is Saved, Then Saved Again, and Again…
Backup software services save data in case of a loss. Part of the service also includes setting up a system that allows users to easily recover that data, should a loss occur.
Ever lost hours’ (or days’) worth of work because you weren’t properly synced, or your computer crashed? It’s the worst.
Every night, our team backs up every piece, packet, and line of data. And with Right Networks Cloud Premier, our award-winning outsourced technology service for CPA firms, those back ups increase from nightly to hourly.
This saves our customers from having to spend hours redoing work after accidental deletions, natural disasters and (let’s be honest) human error.
5. Encryption Protects Data by Making It Indecipherable To Unauthorized Users
Drive encryption protects information by encoding or scrambling text, making it unreadable to unauthorized users.
Keeping data encrypted at the highest level ensures information is inaccessible. And, if a hacker gained access to a cloud hosting provider’s data, they’d view a completely undecipherable hodgepodge. Simple as that.
6. Cloud Hosting Creates a Secure Pathway for Accessing Apps, Software Files and Data
Remote Access Services use a combination of hardware and software that enables users to securely connect to their business’s information via internet connection.
The Right Networks Cloud was built for users to securely connect to their businesses’ software and applications from any internet-connected device. It’s why our customers weren’t Frankenstein-ing together a remote-access solution back in March—they already had it.
Advanced Security Requires Minimal Effort
Human error is still the prevailing cause of data breach incidents.
Why is that? (See first sentence.)
The simplest way to help keep data secure is by using a cloud hosting provider.
And unless you automatically knew what a “Bastion Host Configuration” was after reading through the section on firewalls—I’d bet you’d be happy to scrap the stress of maintaining a secure environment.
Let the nerds who absolutely adore configuring bastion hosts* give you one less thing to think about. They did go to school to learn everything about cybersecurity, after all.
*The actual definition of “bastion host configurations” for all the other curious, tech-loving, non-security majors like me:
A bastion host is a special-purpose computer on a network specifically designed and configured to withstand attacks. The computer generally hosts a single application, e.g. a proxy server, and all other services are removed or limited to reduce the threat to the computer.1