Protected vs. Positioned: The Security Shift Every Bookkeeping Firm Needs to Make
Key Takeaways
- Protected means you’ve covered the basics. That matters, but it’s the floor, not the ceiling.
- A secure SaaS stack requires centralized access management, not individual app oversight. MFA and SSO enforced across every tool close the gaps that manual processes leave open.
- Credential cloaking gives your team access without exposure. When someone leaves, there’s nothing in their inbox or browser to compromise a client account.
- Lingering access from poor offboarding is one of the most common, and most overlooked, security risks bookkeeping firms face.
- Oversight for offshore and outsourced teams doesn’t mean restricting who you can work with. It means building the architecture that makes that work safe and auditable.
- Firms that can answer client questions about data access clearly and confidently hold a competitive advantage most firms can’t claim yet.
Bookkeeping and CAAS firm owners understand better than most that security isn’t optional. You’re handling sensitive financial data, managing client access across multiple platforms, and operating in an environment where a single breach can do serious damage to client trust and your firm’s reputation.
Most firms have the basics covered. But there’s a meaningful difference between having the basics covered and having the right foundation in place.
Security as protection is reactive. It’s what you put in place to avoid disaster.
Security as infrastructure is intentional. It’s what you build to streamline operations, scale with confidence, and grow without second-guessing every hire or handoff.
This post covers the four areas where that shift matters most, and what it looks like in practice to move your firm from protected to positioned.
Is Your Security an Afterthought?
When security gets added reactively, it tends to accumulate in layers. A password manager here, MFA turned on for one platform there, an offboarding checklist that someone remembers to run most of the time. Each piece was added for a good reason. But together, they don’t form a system.
The firms that scale sustainably have made a different choice. They’ve stopped treating security as a set of individual safeguards and started treating it as the architecture their operations run on. The result isn’t just better protection. It’s a firm that’s easier to manage, faster to onboard, and more credible with clients who are asking harder questions about where their data lives and who can see it.
Below are the four areas where that shift shows up most clearly.
A Secure SaaS Stack for Bookkeepers
The average bookkeeping firm runs on a significant number of SaaS apps: accounting software, document storage, payroll platforms, communication tools, time tracking, and project management. Each one is managed slightly differently. And in many firms, almost none of them are talking to each other about access.
In practice, access gets added piecemeal and removed inconsistently. The list of who has access to what across your entire stack is probably in nobody’s head right now, including yours. That’s not a criticism. It’s how these stacks grow.
“Managing” Your SaaS Stack vs. Having it Under Control
| Protected | Positioned |
|---|---|
| “We have MFA turned on and someone on the team manages app access as people join and leave the team.”
Why it’s not enough: Inconsistent coverage, no central view, and manual entry leave gaps that multiply as your team grows. |
|
Quick wins of an in-sync SaaS stack
When your stack is configured to match the way you operate, onboarding takes minutes and offboarding takes seconds. The cognitive load of mentally tracking access across ten different systems disappears, and you get that mental space back to actually run the firm.
In-Control Credential Management
Every bookkeeping firm manages dozens, and sometimes hundreds, of client logins. The question isn’t whether you have a system for handling them. It’s whether that system is working for your firm or quietly working against it.
Password chaos doesn’t usually announce itself as a security problem. It shows up as a team member messaging at 4 p.m. asking for a login, a ten-minute detour before a job can start, or that low-grade anxiety about what’s saved in whose inbox. The cost is time, trust, and mental overhead every day.
| Protected | Positioned |
|---|---|
| “We use a password manager and share logins with the team when they need access.”
Why it’s not enough: Manual distribution means credentials are copied, stored, and remembered in places you can’t control, and there’s no log of who accessed what, or when. |
|
Getting out from under credential chaos
When credentials are cloaked, your team gets the access they need without ever holding the actual password.
They click, they’re in, and the system logs it. If they leave tomorrow, there’s nothing in their inbox, their browser, or their memory that could compromise a client account. The efficiency payoff is immediate, and the security benefit comes along with it.
Safe Onboarding and Offboarding
Bookkeeping firms today run on a rotating roster of seasonal staff, project contractors, virtual assistants, and offshore bookkeepers. Getting people productive quickly is how the firm runs. But access granted in a hurry rarely gets removed with the same urgency.
It lingers. And lingering access is one of the most common and overlooked ways firms quietly expose themselves and their clients.
| Protected | Positioned |
|---|---|
| “We walk new hires through the tools they need and remove their access when they leave.”
Why it’s not enough: This approach is manual and app-by-app, so it’s easy to miss one, hard to verify it’s complete, and impossible to prove after the fact if a client asks. |
|
Expand the team, not the risk
The goal isn’t just to be more secure. It’s to stop spending time on access management at all. When a client asks, “Who has access to our books?” you want to answer with confidence, not spend twenty minutes mentally retracing every contractor you’ve worked with this year.
Oversight for Offshore and Outsourced Teams
Outsourcing and offshoring make smart business sense. They extend your capacity, reduce costs, and let smaller firms compete at a level that simply wasn’t possible a decade ago. The hesitation most firm owners feel isn’t about the quality of the work. It’s about visibility.
When your team is working from devices and networks you can’t see, in locations you can’t directly oversee, how do you stay in control? The answer isn’t to pull back from outsourcing. It’s to build the right architecture around it.
| Protected | Positioned |
|---|---|
| “Our offshore team only has access to the client files relevant to their work.”
Why it’s not enough: File access isn’t the same as credential control. Without cloaked logins and a secure cloud environment, data can still be downloaded, stored, or accessed in ways you can’t see or audit. |
|
Earn the reputation that sets you apart
There’s a client conversation that comes with this, too. More clients are asking direct questions: Who has access to our financials? Where are they located? What controls are in place? A firm that can answer those questions clearly isn’t just more secure. It’s more trusted. That’s a competitive advantage most firms can’t claim yet.
Protected Is the Floor, Not the Ceiling
Protected means you’ve covered the basics. That matters, but it’s the floor, not the ceiling.
Positioned means your security is doing work beyond keeping threats out. It simplifies how your team operates, makes it easier to bring on offshore help, gives you instant visibility and control, and lets you answer client questions about data access without hesitation.
The firms that scale sustainably aren’t just better protected than their peers. They’re built differently. Security isn’t something they bolt on when something goes wrong. It’s part of how the firm runs every day.
That’s the shift from protected to positioned. And once you make it, you’ll wonder how you ran your firm without it.
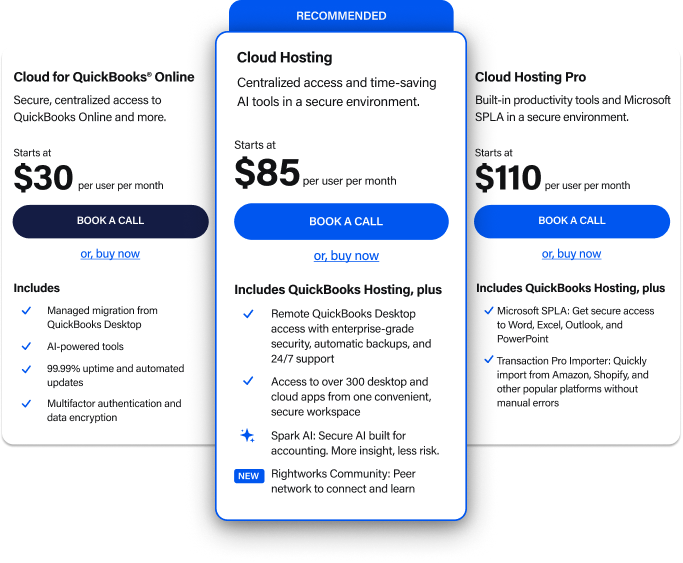
Learn how Rightworks is helping bookkeeping firms like yours stay safe, connected, and ready to work.